The Invisible Signature
Every sound you make online, a voice clip, a stream, a meeting, carries a fingerprint. Not the kind you leave on glass, but the kind you leave in frequency. It’s invisible, persistent, and mathematically unique. And once captured, it never forgets you.
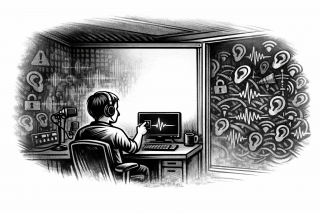
I believe audio fingerprinting is the quietest form of tracking. No cookies, no pixels, no consent banners, just your voice turned into data.
How It Works
Fingerprinting doesn’t care about what you say. It cares about how you sound.
It measures:
- Harmonic patterns
- Microphone noise
- Codec artifacts
- Device‑specific distortions
Together, these form a signature that can identify you across platforms, even when you change accounts.
“Your voice is your username, whether you typed it or not.”
Why It’s Hard to Defeat
You can’t encrypt a frequency. You can only distort it.
But distortion has a cost, clarity. And clarity is what every communication system optimizes for. So the system itself fights your privacy.
The more you try to hide, the more the algorithms notice the anomaly.
Defeating the Fingerprint
You don’t defeat fingerprinting with tools. You defeat it with context control.
- Use controlled environments — same room, same noise floor, same predictable interference.
- Inject randomness — subtle background sounds, low‑level white noise, or dynamic filters.
- Avoid cloud voice processing — local record, local encode, local transmit.
- Rotate devices — each hardware change resets the acoustic baseline.
- Never reuse the same audio chain for identity and activity.
This isn’t paranoia. It’s protocol.
The Philosophy of Silence
Sometimes the best defense is not distortion, it’s absence. Don’t speak when you don’t need to. Don’t stream when you don’t have to. Don’t record what doesn’t need to exist.
Silence is not weakness. It’s the only untrackable signal.
“Noise is traceable. Silence isn’t.”
The Practical Reality
You can’t erase your voice from the internet. But you can stop feeding it.
The practical model:
- Speak offline
- Record locally
- Transmit minimally
- Delete aggressively
Audio fingerprinting thrives on abundance. Starve it.