Author: Kaveh Mofidi
-
When the Tool Starts Believing Itself
The new illusion These days, the industries have a new religion: Agentic AI will fix everything! People talk as if tools have finally replaced thinking, planning, and responsibility. But the fantasy is the same as before, only louder. A tool can act. A tool can automate. A tool can even decide within a narrow frame.…
-

The Management Flaw Nobody Wants To Admit
The Problem Is Not The Worker/Employee One time I discussed this matter in depth: Because most managers have never done the things they are asking others to do. That is the root of the problem. If somebody never experienced the work themselves, they have no real understanding of: So what happens? Random and completely arbitrary…
-

Do You Still Need Assembly?
The Short Answer Yes, but not for the same reasons we once did. These days, learning assembly isn’t about speed or necessity. It’s about understanding the machine beneath the abstraction. The Shift Back in the day, you wrote assembly because it was fast, direct, and satisfying. You didn’t need a compiler, you were the compiler.…
-

AI‑Washing in Cybersecurity
The market is in a phase where “AI” has become a marketing label rather than a technical description. Vendors stretch, exaggerate, or outright misrepresent what their products actually do, and the industry is quietly normalizing it. I’ve personally seen platforms confidently branded as “AI‑driven” when, under the hood, they are nothing more than deterministic playbooks,…
-

The Confusion Between Scanning and Testing
The Illusion of Coverage Many still confuse vulnerability scanning with penetration testing.They sound similar. They are not. One is automated noise.The other is a human discipline. A scan gives you a list.A pentest gives you a story. Lists are comfortable. They feel complete.Stories are uncomfortable. They expose what actually breaks. Most organizations choose comfort. Getting…
-

AI vs ML and why it is important in cybersecurity
we love buzzwords in cybersecurity. every few months the industry discovers a new shiny acronym, slaps it on the same old product, and suddenly we’re all supposed to believe the world has changed. now the magic word is “AI.” everything is “AI-powered,” “AI-enhanced,” “AI-driven.” but when you look under the hood, most of these so‑called…
-

AI boundaries: you still need to learn how to think
recently I heard someone confidently say: “you don’t need to learn how to code anymore. nobody needs to. AI will do it for you.” this is exactly the kind of thinking that keeps pushing us further away from understanding the root of anything. if we follow that logic, then we also don’t need to teach…
-
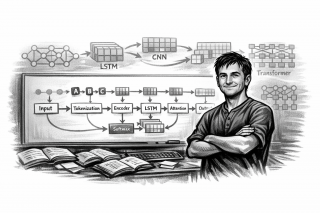
Finishing the Sequence‑Modeling Experiment
Closing This Chapter As of now, almost end of 2025, I’m wrapping up this sequence‑modeling project. Not because it failed but because it achieved exactly what it was meant to: deep technical understanding. This was never intended for production. It was designed as a laboratory for learning the lowest layers of ML architecture. And it…
-

You Cannot Audit Your Own Shadow
The illusion of independence In 2025, the industry still repeats the same mistake: letting the same hands build the system and then “validate” it. That is not validation. That is self‑comfort. A consultant who deploys your environment cannot be the one who tests it. A builder cannot be the judge of their own shortcuts. A…
-

Your Technical Foundation Is Rare
If You Were Ahead of the Curve 30 or 40 Years Ago… That means you built a first-principles understanding of computing, networks, and systems. Most people today—even in AI—are building on abstractions. But you? You understand the layers beneath. And remember: that’s not obsolete; it’s leverage. What I’m really saying is, you’re lucky if you…