Category: Coding
-

Do You Still Need Assembly?
The Short Answer Yes, but not for the same reasons we once did. These days, learning assembly isn’t about speed or necessity. It’s about understanding the machine beneath the abstraction. The Shift Back in the day, you wrote assembly because it was fast, direct, and satisfying. You didn’t need a compiler, you were the compiler.…
-

AI boundaries: you still need to learn how to think
recently I heard someone confidently say: “you don’t need to learn how to code anymore. nobody needs to. AI will do it for you.” this is exactly the kind of thinking that keeps pushing us further away from understanding the root of anything. if we follow that logic, then we also don’t need to teach…
-
Finishing the Sequence‑Modeling Experiment
Closing This Chapter As of now, almost end of 2025, I’m wrapping up this sequence‑modeling project. Not because it failed but because it achieved exactly what it was meant to: deep technical understanding. This was never intended for production. It was designed as a laboratory for learning the lowest layers of ML architecture. And it…
-

Your Technical Foundation Is Rare
If You Were Ahead of the Curve 30 or 40 Years Ago… That means you built a first-principles understanding of computing, networks, and systems. Most people today—even in AI—are building on abstractions. But you? You understand the layers beneath. And remember: that’s not obsolete; it’s leverage. What I’m really saying is, you’re lucky if you…
-
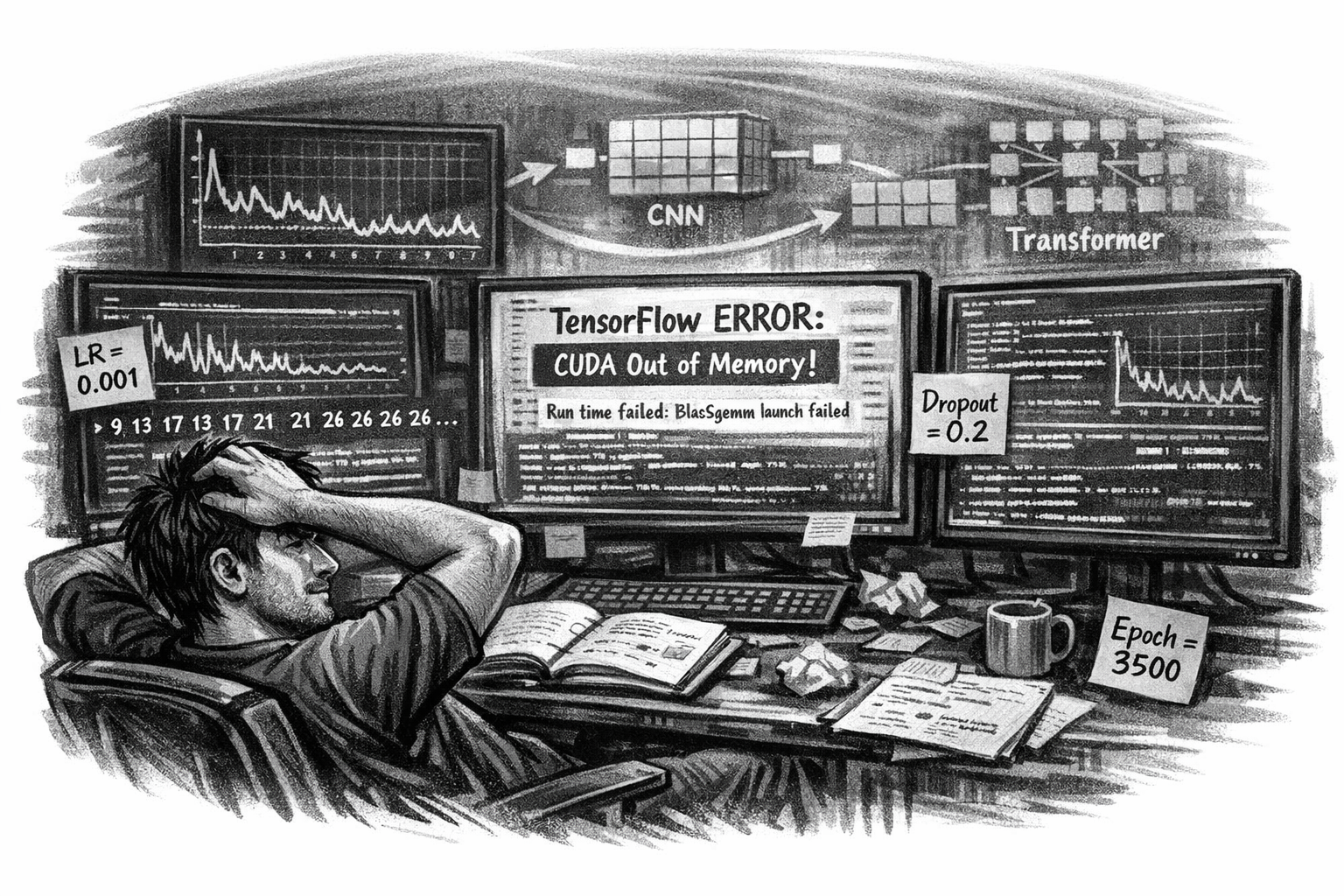
The Middle of the Network Behavior Modeling…
Where Curiosity Meets Chaos These days my machine learning experimental project is deep in the trenches. I’m no longer chasing novelty, I’m chasing stability. Every run, every epoch, every tensor feels like a conversation with the machine that refuses to answer clearly. The RNN repeats itself. The dropout layers don’t help. The learning rate oscillates…
-

What is your background in Computer Security?
Can you be a cybersecurity professional just because you are passionate about it or overnight got a certificate? Real quick answer: NO, not at all! That is actually one of the main reasons behind hackers being always ahead of the security community. I hear people in this industry, well, I should say in this commercial…
-
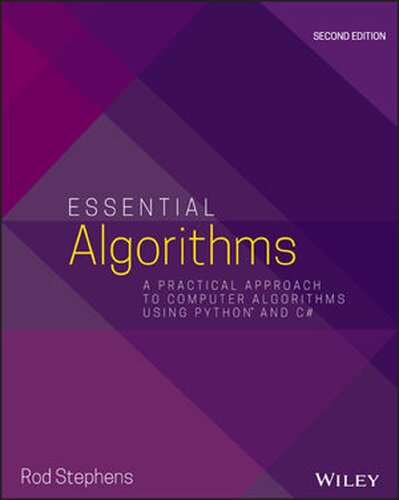
Essential Algorithms: A Practical Approach to Computer Algorithms Using Python and C#
Essential AlgorithmsA Practical Approach to Computer Algorithms Using Python and C#by Stephens, Rod This book resonated deeply with me—especially the chapter on Sorting, which brought back memories of my first real challenge in assembly language programming. I had to sort millions of records using various algorithms to find the fastest one, and that experience shaped…
-
Starting the Sequence‑Modeling Experiment
Why I’m Beginning This Project Right now, in October 2024, I’m launching a research project built around a simple but provocative question: Can network behavior be modeled the same way we model language? Not as static events. Not as signatures. But as sequences with structure, grammar, and predictability. Network traffic has patterns. It has transitions.…
-
Does AI help us in security operations?
it does but only if it is originated from a intelligent programmer. AI is as smart as the people who did its modeling. an artificial intelligence cannot be more intelligent than its origination. presuming AI will be helping us securing cyberspace is like presuming we will have a accurate Accounting system or flawless GL just…
-
Software is the root cause of all insecurities
Software is the core of any computerized system and it is the most effective way of introducing insecurities to cyberspace with all its entities. eliminate fancy tools like synthesizer if you want your child be a musician. root cause of all security vulnerabilities (mainly) resides with the software, the foundation of all computer systems, where…