SECURE TARGET: A Critical Lens on Tech, Power, and the People Behind It
-
What is research and why is it crucial for elevating your knowledge in computer security?
Doing research in computer security since 1989 has kind of put me in a situation where I could organically learn what research really is and what I expect from it. To start with, perhaps it’s easier to say what is “not” considered research. These days, when people talk about research, they’re simply referring to Googling…
-
The Middle of the Network Behavior Modeling…
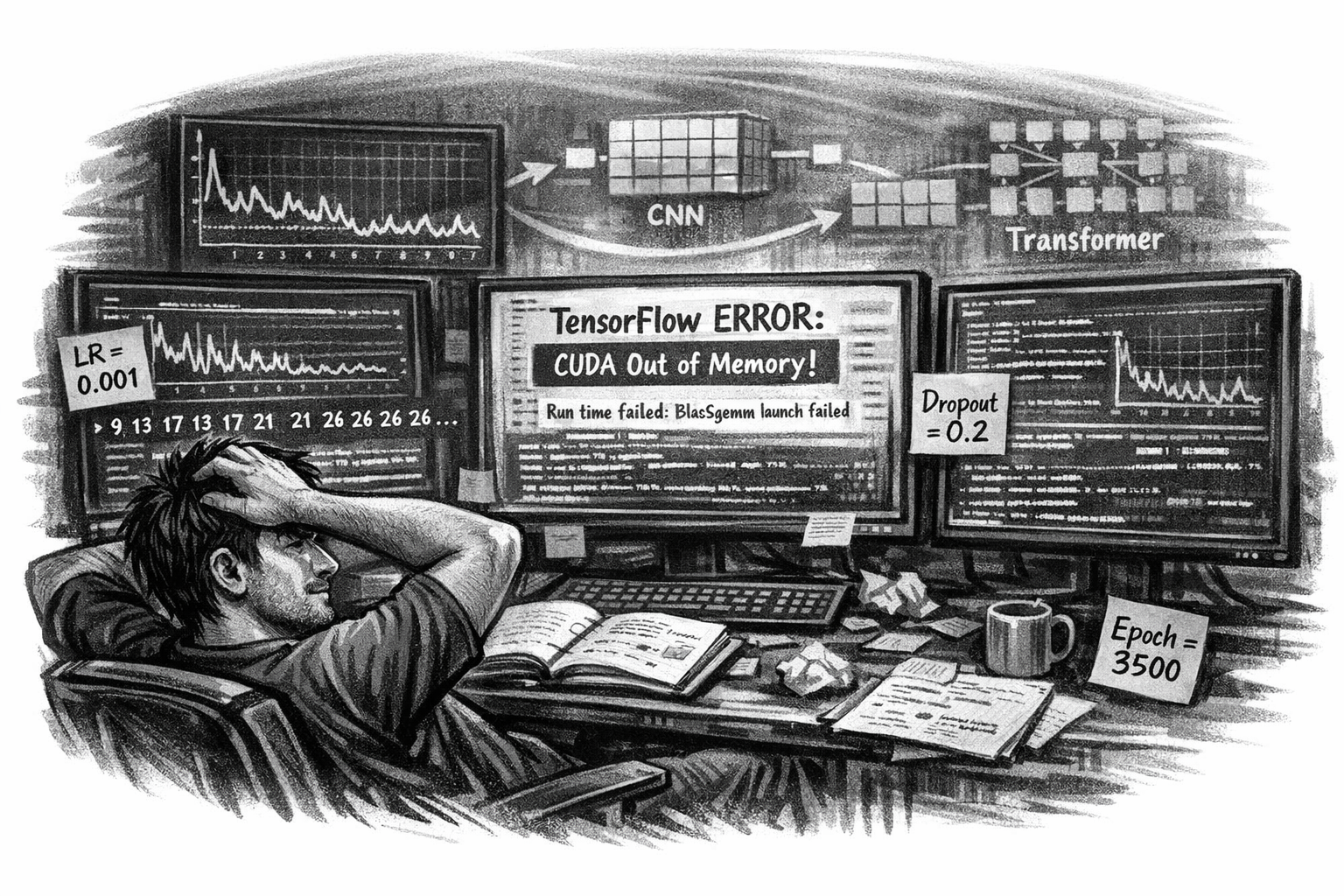
Where Curiosity Meets Chaos These days my machine learning experimental project is deep in the trenches. I’m no longer chasing novelty, I’m chasing stability. Every run, every epoch, every tensor feels like a conversation with the machine that refuses to answer clearly. The RNN repeats itself. The dropout layers don’t help. The learning rate oscillates…
-

When Are You Ready For Agentic AI Security?
The Excitement Is Premature Everyone wants agentic AI in security. Autonomous actions. Self-healing systems. Machines making decisions… Sounds efficient. Sounds inevitable. But are you ready? Or are you just tired of doing the work yourself? “Automation without understanding is just faster confusion.” The Missing Foundation It may sound strange, but if you have never experienced…
-

What is your background in Computer Security?
Can you be a cybersecurity professional just because you are passionate about it or overnight got a certificate? Real quick answer: NO, not at all! That is actually one of the main reasons behind hackers being always ahead of the security community. I hear people in this industry, well, I should say in this commercial…
-
Agentic AI vs. AI agent: why the confusion will cost you
You probably think they are the same thing. They are not. And if you are a security practitioner or a strategic thinker, the difference is not academic, it is operational. What most people get wrong An AI agent is a component. It is a model that perceives input and produces output. Think of it as…
-

AI Stuff
…Generations have already lost their Appetite to Learn, to Explore, and to Cherish the Beauty of Science and True Knowledge, let alone Pursuing Wisdom… First of all, I think we excessively use the term “AI” irrelevantly; most of the time, I mean the term “artificial intelligence” is being overly used in a way that is…
-
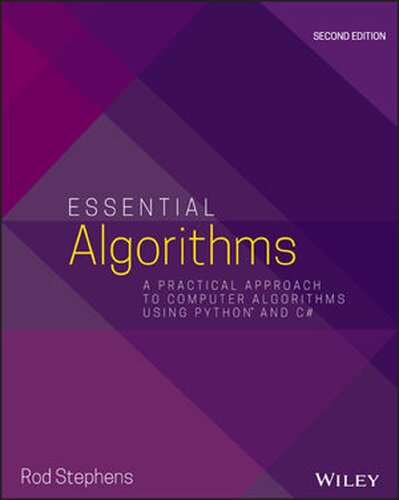
Essential Algorithms: A Practical Approach to Computer Algorithms Using Python and C#
Essential AlgorithmsA Practical Approach to Computer Algorithms Using Python and C#by Stephens, Rod This book resonated deeply with me—especially the chapter on Sorting, which brought back memories of my first real challenge in assembly language programming. I had to sort millions of records using various algorithms to find the fastest one, and that experience shaped…
-

The Art of Machine Learning: A Hands-On Guide to Machine Learning with R
The Art of Machine Learning: A Hands-On Guide to Machine Learning with Rby Norman Matloff (Author) I have a strong opinion about this book, and obviously it did not meet my expectations. I am just going to highlights several key areas where I believe the book falls short, including the lack of relevant information, disorganized…
-

Who do you think is going to be the winner, the hacker or the security practitioner?
Who do you think is going to be the winner, the hacker or the security practitioner? This question is in the same ballpark as: Do we need more cybersecurity professionals who are getting more and more certifications? Then why are we just getting weaker compared to the hacker’s community? For example, is the ability to…
-
Starting the Sequence‑Modeling Experiment
Why I’m Beginning This Project Right now, in October 2024, I’m launching a research project built around a simple but provocative question: Can network behavior be modeled the same way we model language? Not as static events. Not as signatures. But as sequences with structure, grammar, and predictability. Network traffic has patterns. It has transitions.…